Table of Contents >> Show >> Hide
- What Root Privileges Mean on a Mac
- When You Might Need to Open an App as Root
- Before You Open Anything as Root, Try These Safer Alternatives
- How to Open an App with Root Privileges on a Mac
- Why sudo open -a AppName Is Not Always the Answer
- Common Problems You May Run Into
- Best Practices for Opening Apps with Root Privileges
- Common Real-World Experiences Mac Users Run Into
- Conclusion
- SEO Tags
Mac users love a clean interface, a smooth workflow, and the comforting illusion that nothing terrible can happen if you just click the shiny thing carefully enough. Then one day, an app refuses to touch a protected file, a utility insists you do not have permission, or a maintenance task suddenly demands the kind of authority normally reserved for ancient wizards and IT admins. That is when the phrase root privileges enters the chat.
If you are trying to open apps with root privileges on a Mac, the short answer is this: yes, it can be done, but it is not something you should treat like a keyboard shortcut for everyday life. Modern macOS is designed to make full-root app launching uncommon, sometimes awkward, and often unnecessary. In many cases, the smarter move is to adjust permissions, grant the right privacy access, or use a built-in authentication prompt instead of turning an entire app loose with superuser power.
Still, there are legitimate reasons to do it. Maybe you need to edit a protected configuration file, run a legacy admin utility, or troubleshoot a tool that requires elevated access. This guide explains how root privileges work on macOS, the safest ways to open apps with elevated rights, what usually goes wrong, and when you should back away slowly and let the system protect itself.
What Root Privileges Mean on a Mac
On macOS, the root user is the superuser account. It has broad read and write access across the system and can perform actions that standard users and even many administrator-level actions cannot do directly. That sounds powerful because it is. It also sounds risky because, again, it is.
Here is the important distinction: an administrator account is not the same thing as the root account. An admin account can approve privileged actions with authentication. The root account has unrestricted power over many parts of the system. In plain English, an admin gets the keys to the building when needed, while root is basically the building inspector, landlord, and demolition crew all rolled into one.
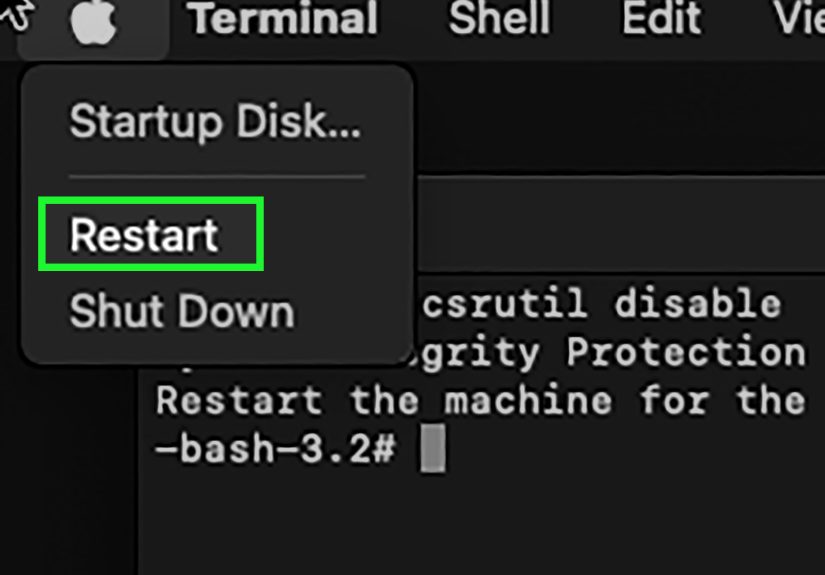
That is why macOS does not encourage logging in as root for routine tasks. For most legitimate workflows, Apple expects administrators to use sudo in Terminal for a specific command instead of permanently enabling the root user or trying to run everything with maximum privileges.
When You Might Need to Open an App as Root
There are a few real-world situations where opening an app with root privileges makes sense:
- Editing protected system-owned files with a text editor
- Running a maintenance or repair utility that needs elevated access
- Using an older admin tool that was designed before current macOS security behavior became stricter
- Troubleshooting file ownership and permission issues in system locations
That said, many tasks that look like “I need root” are actually “I need the right permission.” If an app cannot access your Desktop, Documents, Downloads, external disk, or Full Disk Access-protected areas, launching it as root may not be the clean fix you think it is. Sometimes the better solution is granting the correct privacy permission in System Settings, changing ownership, or authenticating through the normal macOS prompt.
Before You Open Anything as Root, Try These Safer Alternatives
1. Use the Built-In Authentication Prompt
Many Mac apps and installers already know how to request elevated privileges when needed. If the app is properly designed, it will prompt for an administrator name and password at the point where elevated access is required. That is better than launching the entire app as root because it limits how much power the app gets and when it gets it.
2. Fix File and Folder Permissions
If the problem is access to a file, folder, or disk, check the item’s permissions in Finder. Sometimes the issue is simply that your account does not have read/write access, the owner is wrong, or a permissions mismatch is blocking the app. Changing the permissions is often cleaner than elevating the whole application.
3. Grant Privacy Access
macOS privacy controls are strict for a reason. An app might need Full Disk Access, Files and Folders permission, or another Privacy & Security approval to work properly. If a tool fails with “operation not permitted,” that may be a privacy control problem rather than a pure root problem.
4. Use the Terminal Tool Instead of the GUI App
If you only need to perform one protected action, the command-line version may be the smarter path. Running a single command with sudo is usually safer and more predictable than launching an entire graphical application as root and hoping it behaves politely. Software does not always become more trustworthy just because it looks nice in a window.
How to Open an App with Root Privileges on a Mac
Now for the part everyone came here for. There are a few methods, but only one is typically reliable for GUI apps.
Method 1: Run the App’s Executable from Terminal
This is the most direct approach when you truly need to launch a macOS app with elevated privileges. App bundles on macOS are really folders that contain the actual executable inside them. Instead of launching the app the normal way, you run the executable itself with sudo.
Basic syntax:
Example:
After pressing Return, Terminal will ask for your administrator password. Type it and press Return again. Remember that your password does not appear on screen while typing. This is normal behavior, not a dramatic betrayal by your keyboard.
This method works because you are executing the app binary directly as a privileged process. It is far more reliable than assuming every GUI app will inherit root privileges simply because you launched it through a helper command.
Method 2: Open a Specific File in a Context That Needs Privileges
Sometimes you do not need the whole app running as root. You just need to work with one protected file. In those cases, the better route is often to use a Terminal-based editor or a more precise administrative workflow rather than elevating an entire GUI editor.
For example, if you need to edit a protected configuration file, using a Terminal editor with sudo can be safer than launching a graphical text editor as root. It gives you a narrower scope and less chance of accidentally dragging, saving, or replacing the wrong thing.
Method 3: Use a Privileged Helper if You Are a Developer
If you are building a Mac app and need certain operations to run with higher privileges, the modern best practice is not “make the whole app root and hope for the best.” The better design is to keep the main GUI app running normally and use a privileged helper or daemon only for the small set of tasks that actually require elevation.
This is more secure, more maintainable, and much more aligned with how current macOS expects privileged operations to be handled. For developers, this is the grown-up version of privilege management. For everyone else, it is a reminder that running an entire GUI app as root is usually more of a workaround than a best practice.
Why sudo open -a AppName Is Not Always the Answer
A lot of Mac users search for a one-line trick like this:
It looks elegant. It feels elegant. It is not always actually doing what people think.
The problem is that the open command tells Launch Services to open the application in your user session. That does not consistently translate into the app itself running with true root privileges. In practice, this means the command may launch the app, but the app may still behave like a normal user-space process for many purposes.
That is why directly executing the binary inside the app bundle is the more dependable method when real elevation is required. The “pretty” version is tempting, but the ugly version is often the truthful one.
Common Problems You May Run Into
The App Opens but Still Cannot Access Everything
Welcome to modern macOS. Even when you elevate a process, privacy protections and security frameworks can still affect what the app can do. Root access does not magically erase every rule in the system.
The App Crashes or Behaves Strangely
Some apps were never designed to run as root. Sandboxed apps, App Store apps, and utilities built with modern security assumptions may not behave correctly when forced into a privileged context. Menus may work, but file dialogs fail. The window opens, but the expected action still does not happen. This is the operating system’s way of saying, “Technically yes, practically no.”
You Get “Operation Not Permitted” Errors
This usually points to macOS privacy controls, not a simple admin-rights issue. The app or Terminal may need Full Disk Access or another approved privacy permission. If you skip that and go straight to brute-force elevation, you can spend a long time troubleshooting the wrong problem.
The App Is Blocked from Opening
If the app is unsigned, improperly signed, quarantined, or blocked by Gatekeeper, launching it as root is not the right first fix. You should verify that the app is trusted and approved through normal macOS security flows. Opening random software with maximum privileges is a great way to turn one small inconvenience into a very educational disaster.
Best Practices for Opening Apps with Root Privileges
- Use root only for specific, legitimate administrative tasks
- Prefer
sudofor one action over enabling the root account - Launch the executable directly if true elevation is required
- Do not assume
sudo open -agives reliable full-root behavior - Check file permissions and privacy settings before escalating
- Avoid running everyday apps as root just because it “works faster”
- Quit the elevated app as soon as the task is complete
The golden rule is simple: use the smallest amount of power necessary. On a Mac, that is not just good housekeeping. It is good security.
Common Real-World Experiences Mac Users Run Into
One of the most common experiences is pure confusion. A user tries to edit a protected file, launches the app normally, and gets a permission error. Then they try again with an administrator account and assume that should be enough. When it still fails, the natural reaction is to think macOS is being difficult for sport. In reality, the system is separating ordinary admin approval from full-root execution and then layering privacy protections on top. It feels inconsistent until you understand that macOS is guarding different doors with different locks.
Another common experience is the false victory. The app opens after a Terminal command, so the user assumes success. But when they actually try to save a change, install a helper, or access a protected folder, the action still fails. This is where many people discover that launching an app and launching it properly with the exact privileges it needs are not the same thing. It is also where users start learning the difference between file permissions, admin authentication, Full Disk Access, and true root execution.
There is also the “I only needed this one tiny edit” experience. Someone wants to make a quick change to a config file, and suddenly they are reading about app bundles, binary paths, Terminal syntax, and security warnings that sound like they were written by a very disappointed attorney. This is normal. macOS makes deep system changes intentionally inconvenient because convenience is not the top priority when system integrity is on the line.
Power users often describe a learning curve that goes something like this: first they try to force everything with root, then they break something small, then they become dramatically more respectful of targeted privilege use. After a while, they stop asking, “How do I run this entire app as root?” and start asking, “What exact action needs elevation?” That is usually the moment they become better Mac troubleshooters.
Developers have their own version of this experience. They build a Mac app, discover that a certain task needs elevated rights, and initially think the whole app should just run with more privilege. Later, they learn that the cleaner model is a normal app plus a narrowly scoped privileged helper. It is a bit more work up front, but it avoids a long list of security and compatibility headaches down the road.
Perhaps the most relatable experience of all is realizing that the system was right to be cautious. Many Mac users eventually discover that the issue was not “I need root,” but “I need permission to this folder,” or “I need Full Disk Access for Terminal,” or “this app is blocked because it is not trusted yet.” Once that clicks, the whole topic becomes less mystical. Root privileges stop looking like a magic button and start looking like what they really are: a very sharp tool you only reach for when gentler tools are not enough.
Conclusion
Opening apps with root privileges on a Mac is possible, but it is not something modern macOS treats casually. The safest and most reliable method is to launch the app’s internal executable with sudo from Terminal when you genuinely need elevated rights. Even then, you should treat root access as a temporary tool, not a permanent lifestyle choice.
For many tasks, the smarter solution is not to run the entire app as root at all. Adjust permissions, grant the right privacy access, use an administrator prompt, or perform the exact action in Terminal with a single elevated command. In other words, do not bring a flamethrower to light a birthday candle.
If you remember one thing, make it this: on a Mac, elevation is best used with precision. The less power you hand out, the fewer surprises you will have to explain later.