Table of Contents >> Show >> Hide
- What AdGuard Home Does on Linux
- What You Need Before Installation
- Step 1: Download and Install AdGuard Home
- Step 2: Open the Right Firewall Ports
- Step 3: Fix the Port 53 Conflict on Ubuntu
- Step 4: Run AdGuard Home Without Living as Root
- Step 5: Point Your Network to AdGuard Home
- Step 6: Configure Upstream DNS and Filters
- Step 7: Secure the Dashboard and Consider Encrypted DNS
- How to Verify Everything Works
- Common Problems and Fast Fixes
- Best Practices for Long-Term Use
- Final Thoughts
- Real-World Experience: What It Is Actually Like to Use AdGuard Home on Linux
- SEO Tags
If your internet connection feels like a highway full of pop-ups, trackers, and mystery requests from gadgets that definitely do not need to “phone home,” AdGuard Home on Linux is a smart fix. It acts as a network-wide DNS filtering server, which means it can block ads, trackers, and shady domains for every device on your network, not just the laptop that happens to have a browser extension installed.
That is the magic trick. Your Linux machine becomes the quiet bouncer at the door, checking DNS requests before they get into the party. Phones, tablets, smart TVs, game consoles, and that suspiciously chatty smart bulb all benefit. Better yet, Linux is a fantastic host for AdGuard Home because it is stable, efficient, and happy to run on anything from a full server to a tiny mini PC.
In this guide, you will learn how to set up AdGuard Home on Linux, handle the usual port conflicts, configure DNS properly, secure the dashboard, and make the system actually useful in day-to-day life. No fluff, no keyword stuffing, no robotic tutorial voice that sounds like it was written by a microwave manual.
What AdGuard Home Does on Linux
AdGuard Home is a DNS-level filtering service. In plain English, it sits between your devices and the wider internet when those devices try to look up domain names. Instead of letting every tracking or advertising domain pass through freely, AdGuard Home checks requests against filters and rules. If the domain is on the naughty list, the request gets blocked before the connection even starts.
This approach gives you a few big advantages:
- Network-wide ad and tracker blocking.
- One central place to manage DNS for your whole home or lab.
- Visibility through query logs, statistics, and client-level settings.
- Support for encrypted DNS features if you want a more private setup.
- Optional extras such as parental controls, custom rules, and DNS rewrites.
It is not a silver bullet. Some apps use hardcoded DNS, some services bundle ads from the same domains as content, and some devices behave like spoiled celebrities when their preferred DNS is changed. Still, for most home networks, AdGuard Home gives a dramatic improvement with surprisingly little hardware.
What You Need Before Installation
Before you install anything, make sure you have the basics covered:
- A Linux machine that stays on regularly. Ubuntu, Debian, Fedora, Rocky, AlmaLinux, and similar distributions work well.
- A static LAN IP address for the Linux host, or at least a DHCP reservation on your router.
- Access to your router’s DNS or DHCP settings.
- A firewall plan, because DNS that only works for your own feelings is not much use.
If you are using Fedora or a Fedora-based system, install AdGuard Home in /usr/local/bin rather than a random directory. SELinux and permissions can otherwise turn your peaceful evening into a debugging festival.
Step 1: Download and Install AdGuard Home
A common manual setup on Linux looks like this:
On first launch, AdGuard Home usually opens the initial setup wizard on port 3000. From another device on the same network, open:
Complete the wizard, choose the network interface, create the admin account, and confirm the web interface and DNS listening settings.
Once the basic wizard is done, install it as a system service:
Useful service commands include:
At this point, AdGuard Home is no longer just a guest. It has keys to the building.
Step 2: Open the Right Firewall Ports
For a basic installation, the important ports are:
53for DNS3000for the initial setup wizard80for the standard web interface443if you plan to use DNS-over-HTTPS or secure dashboard access853if you plan to use DNS-over-TLS
On Ubuntu or Debian with UFW
On RHEL, Rocky, AlmaLinux, or Fedora with firewalld
If you only want AdGuard Home available inside your LAN, keep those rules limited to local interfaces or trusted zones. Exposing a DNS server carelessly to the internet is a great way to become famous for the wrong reasons.
Step 3: Fix the Port 53 Conflict on Ubuntu
This is the classic Linux setup trap. On many Ubuntu systems, systemd-resolved already uses port 53 through the local stub listener at 127.0.0.53. AdGuard Home then tries to start, bumps into that listener, and politely screams.
Check what is using port 53:
If systemd-resolved is the culprit, create the configuration directory and override file:
Then switch resolv.conf and restart the resolver:
Now restart AdGuard Home and test again. This step alone solves a huge number of “why is Linux being dramatic?” moments.
Step 4: Run AdGuard Home Without Living as Root
Linux admins generally prefer services to run with the least privilege possible. AdGuard Home can do that too. Since DNS normally needs privileged ports, the clean workaround is to grant the binary the required capabilities:
That allows it to bind to port 53 and work with network interfaces without needing full root privileges every time.
If you do not want to grant capabilities, another option is to change the DNS listening port in AdGuardHome.yaml to something above 1024. That is technically valid, but many client devices expect DNS on port 53, so it is usually less practical for a normal home network.
Step 5: Point Your Network to AdGuard Home
Installing AdGuard Home is only half the job. Your devices need to actually use it.
Best option: Change DNS on your router
Log in to your router and set the LAN DNS server to your AdGuard Home machine’s IP address. That way, devices receiving DHCP leases automatically use your new DNS server.
Example:
Then your router hands out 192.168.1.10 as the DNS server to phones, laptops, tablets, and other devices on the network.
Fallback option: Configure clients individually
If the router does not let you set custom LAN DNS, change DNS manually on devices. That works, but it is more tedious and tends to be forgotten the moment somebody buys a new tablet.
Another option: Use AdGuard Home as DHCP server
If your router is stubborn and allergic to customization, AdGuard Home can also act as the DHCP server. In that design, the Linux host hands out IP addresses and DNS settings itself. It is useful, but you should only enable one DHCP server on the network unless you enjoy chaos.
Step 6: Configure Upstream DNS and Filters
Inside the AdGuard Home dashboard, go to DNS settings and choose your upstream resolvers. This is where AdGuard Home sends allowed requests after filtering them.
Good upstream choices usually include privacy-focused or well-maintained public resolvers. Many people prefer Cloudflare, Quad9, or similar services. The exact choice depends on whether you value speed, malware filtering, privacy policy, or regional reliability most.
Then review your filtering settings:
- Enable built-in protection features you actually want.
- Add reputable blocklists, but do not add every list on the internet like you are collecting trading cards.
- Use the query log to find domains that should be unblocked or custom-blocked.
- Create client-specific rules for children’s devices, smart TVs, or test machines.
A lean filter setup is often better than a giant pile of lists that blocks half the modern web and your spouse’s weather app.
Step 7: Secure the Dashboard and Consider Encrypted DNS
The web interface is convenient, but convenience loves to become a security problem when nobody is looking. Start with the basics:
- Use a strong admin password.
- Limit dashboard exposure to your LAN unless you truly need remote access.
- Use a reverse proxy if you already manage web services on the server.
- Prefer HTTPS if you expose the interface beyond a trusted internal network.
AdGuard Home also supports encrypted DNS options such as DNS-over-HTTPS and DNS-over-TLS. If you want clients to connect securely, upload a valid TLS certificate, add the private key, and specify the correct server name in the encryption settings.
This is especially useful when you want mobile devices, laptops, or remote clients to use your resolver more privately. It is also handy if you like your DNS traffic wrapped in a coat instead of wandering around in plain text.
How to Verify Everything Works
Once setup is done, verify before declaring victory on social media.
Test from the server
The first query should resolve normally. The second may return a blocked result depending on your filters.
Test from a client device
- Check the device’s current DNS server.
- Open a few websites that usually contain obvious ads.
- Watch the AdGuard Home query log for live requests.
If you do not see client requests in the dashboard, the device is probably not using AdGuard Home yet. That is not a filtering issue. That is a routing issue wearing a fake mustache.
Common Problems and Fast Fixes
AdGuard Home starts, but devices are not filtered
Usually the router is still handing out your ISP’s DNS or its own DNS forwarder. Recheck DHCP and LAN DNS settings.
The dashboard works, but DNS does not
That usually points to firewall rules, port 53 conflicts, or the wrong listening interface.
Some websites break
Use the query log to find blocked domains and whitelist only what is necessary. Do not disable every filter because one recipe site wanted to autoplay twelve videos.
Fedora throws permission or SELinux errors
Install the binary in /usr/local/bin and review SELinux context and firewalld rules.
Remote encrypted DNS does not work
Double-check your public DNS name, certificate, firewall rules, and whether your reverse proxy is forwarding trusted headers properly.
Best Practices for Long-Term Use
- Give the server a static IP or DHCP reservation.
- Back up
AdGuardHome.yamland the data directory. - Check the dashboard occasionally instead of treating it like a decorative aquarium.
- Update AdGuard Home when stable releases arrive.
- Keep filter lists practical, not excessive.
- Document your router DNS changes so future-you does not have to play detective.
Final Thoughts
Learning how to set up AdGuard Home on Linux is one of those projects that pays off quickly. The install is light, the daily maintenance is low, and the results are immediate across the whole network. Once it is running properly, web pages feel cleaner, smart devices become less noisy, and you gain a much clearer picture of what your network is doing behind the scenes.
The real win is not just ad blocking. It is control. Linux gives you a dependable platform, and AdGuard Home gives you visibility plus filtering at the DNS level. Put them together and you get a setup that is practical, private, and surprisingly satisfying. A tiny Linux box quietly defending your network is the kind of low-drama hero every home lab deserves.
Real-World Experience: What It Is Actually Like to Use AdGuard Home on Linux
After the excitement of installation wears off, the real question is simple: what is it like to live with AdGuard Home on Linux every day? The honest answer is that, once configured correctly, it fades into the background in the best possible way. That is a compliment. Great infrastructure is boring. It works, it stays out of the way, and it only asks for attention when something meaningful changes.
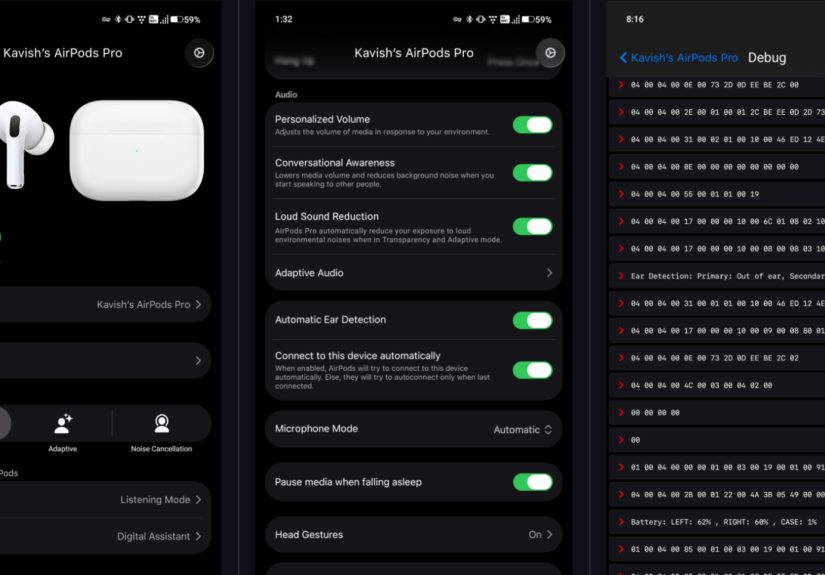
One of the first things people notice is how many devices immediately benefit. You set up one Linux host, point the router to it, and suddenly phones, tablets, laptops, streaming boxes, and smart TVs all start filtering requests through the same DNS service. It feels almost unfair. You do one job once, and half the house gets quieter. Pages load with fewer junk calls, some apps feel less cluttered, and the query log becomes a fascinating peek into what your gadgets are trying to contact all day.
The query log is both helpful and mildly terrifying. It can reveal just how chatty modern devices are. A smart TV may contact analytics domains more often than some people text their friends. A budget Android device can generate a surprising stream of tracking requests. A game console that looks innocent enough may phone home to a small parade of services. AdGuard Home makes this visible in a way that changes how you think about network privacy. It is not abstract anymore. You can actually see the requests.
Linux itself is a great companion for this kind of service. A small Ubuntu or Debian box can run for months with very little fuss. Resource usage is typically light, and even older hardware handles the job without complaining. A lot of users end up running AdGuard Home on a mini PC, a low-power NUC-style machine, or a repurposed old desktop. It does not need flashy hardware. DNS filtering is more about consistency than horsepower.
That said, the setup experience is not always perfectly smooth the first time. The biggest stumbling block is usually DNS already being used by something else, especially systemd-resolved. Once you understand that port 53 is prime real estate and Linux already rented it out to another tenant, the problem makes more sense. After fixing that conflict, the rest of the setup usually feels much easier.
Another real-world lesson is that less is more with blocklists. New users often go through a phase where they add every filter list they can find, as if winning depends on collecting the biggest pile. In practice, too many lists can create false positives, break apps, and make troubleshooting harder. A smaller, well-maintained set of filters usually delivers a better balance of cleanliness and usability.
There is also something satisfying about the maintenance routine. Updating AdGuard Home, checking a few logs, tweaking a client rule, and watching the network stats becomes a simple admin habit rather than a burden. It feels closer to tuning a well-behaved home server than babysitting a fragile application.
Perhaps the best part is the sense of ownership. Instead of handing all DNS decisions to an ISP router and hoping for the best, you are actively managing a useful part of your network. Linux provides the foundation, AdGuard Home provides the control panel, and together they create a setup that feels both practical and empowering. Once you have used it for a while, going back to an unmanaged network feels a bit like taking the batteries out of your smoke detector and saying, “Eh, probably fine.”